
Get Eccouncil ECSAv10 Exam Dumps
Eccouncil Certified Security Analyst (ECSA) v10 Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

ECSAv10 Desktop Practice
Test Software
Total Questions : 201

ECSAv10 Questions & Answers
(PDF)
Total Questions : 201

ECSAv10 Web Based Self Assessment Practice Test
Following are some ECSAv10 Exam Questions for Review
Mason is footprinting an organization to gather competitive intelligence. He visits the company's website for contact information and telephone numbers but does not find any. He knows the entire staff directory was listed on their website 12 months. How can he find the directory?
SQL injection attacks are becoming significantly more popular amongst hackers and there has been an estimated 69 percent increase of this attack type.
This exploit is used to great effect by the hacking community since it is the primary way to steal sensitive data from web applications. It takes advantage of non-validated input vulnerabilities to pass SQL commands through a web application for execution by a back-end database.
The below diagram shows how attackers launched SQL injection attacks on web applications.
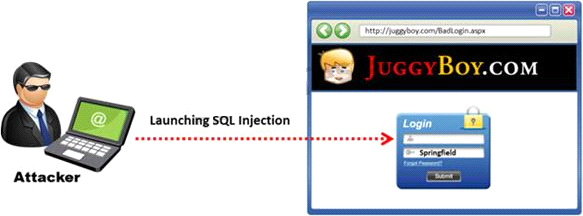
Which of the following can the attacker use to launch an SQL injection attack?
Jim performed a vulnerability analysis on his network and found no potential problems. He runs another utilitythat executes exploits against his system to verify the results of the vulnerability test. The second utilityexecutes five known exploits against his network in which the vulnerability analysis said were not exploitable.
What kind of results did Jim receive from his vulnerability analysis?
Windows stores user passwords in the Security Accounts Manager database (SAM), or in the Active Directory database in domains. Passwords are never stored in clear text; passwords are hashed and the results are stored in the SAM.
NTLM and LM authentication protocols are used to securely store a user's password in the SAM database using different hashing methods.
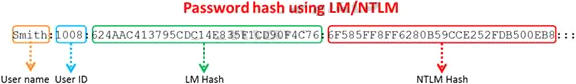
The SAM file in Windows Server 2008 is located in which of the following locations?
Which among the following information is not furnished by the Rules of Engagement (ROE) document?
Unlock All Features of Eccouncil ECSAv10 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support