
Get Eccouncil 312-96 Exam Dumps
Eccouncil Certified Application Security Engineer (CASE) JAVA Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

312-96 Desktop Practice
Test Software
Total Questions : 47

312-96 Questions & Answers
(PDF)
Total Questions : 47

312-96 Web Based Self Assessment Practice Test
Following are some 312-96 Exam Questions for Review
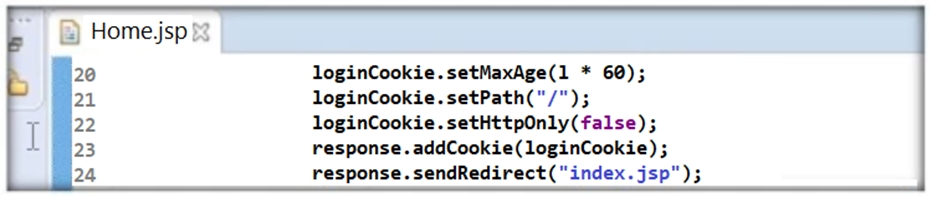
Thomas is not skilled in secure coding. He neither underwent secure coding training nor is aware of the consequences of insecure coding. One day, he wrote code as shown in the following screenshot. He passed 'false' parameter to setHttpOnly() method that may result in the existence of a certain type of vulnerability. Identify the attack that could exploit the vulnerability in the above case.
Identify what should NOT be catched while handling exceptions.
A EOFException
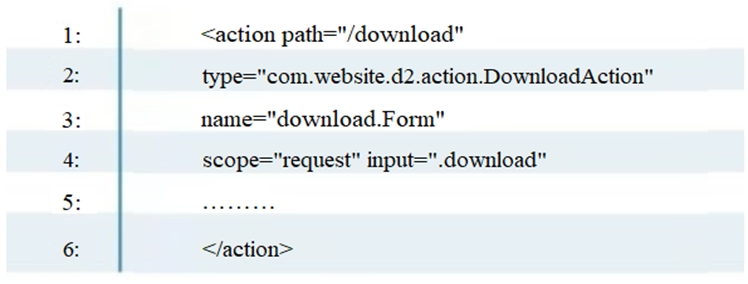
To enable the struts validator on an application, which configuration setting should be applied in the struts validator configuration file?
Which of the following relationship is used to describe abuse case scenarios?
It is recommended that you should not use return, break, continue or throw statements in _________
Unlock All Features of Eccouncil 312-96 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support