
Get McAfee MA0-107 Exam Practice Questions - Real and Updated
McAfee Endpoint Security Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

MA0-107 Desktop Practice
Test Software
Total Questions : 70

MA0-107 Questions & Answers
(PDF)
Total Questions : 70

MA0-107 Web Based Self Assessment Practice Test
Following are some MA0-107 Exam Questions for Review
While tuning the firewall policy, the ePO administrator notices unauthorized traffic is being initiated by a file transfer utility application. If this is a recently approved application, in which of the following locations should this be configured to allow FTP traffic only with this application?
The network operations team has configured the company's VPN connector to deny connectivity if virus scan definitions are older than seven days. In order for a user to immediately meet the VPN connector's policy, which of the following should the administrator enable?
Security operations has recently received indicators of compromise (IOCs) detailing a new piece of malware for which coverage is not available. The threat advisory recommends a list of file paths and registry keys to prevent this new malware from successfully executing. Which of the following ENS 10.5 features should be used to achieve this goal?
An ePO administrator wants to enable script scanning in the environment; however, the administrator wants to exclude several custom scripts from being scanned. Which of the following is the BEST practice for script scan exclusions?
An engineer needs to allow a specific application to run. The engineer just finished creating an Exploit Prevention process exclusion. After applying the exclusion, the engineer notices the application is not being run. The following information is provided to the engineer:
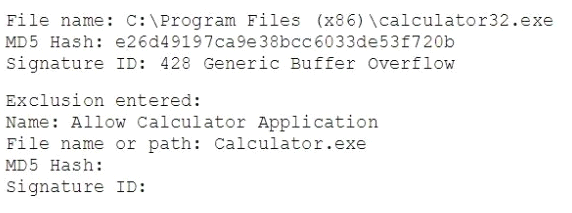
Which of the following is the error with the engineer's exclusion?
Unlock All Features of McAfee MA0-107 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support













