
Get Nutanix NCM-MCI-5.15 Exam Dumps
Nutanix Certified Master - Multicloud Infrastructure (NCM-MCI) 5.15 Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

NCM-MCI-5.15 Desktop Practice
Test Software
Total Questions : 107

NCM-MCI-5.15 Questions & Answers
(PDF)
Total Questions : 107

NCM-MCI-5.15 Web Based Self Assessment Practice Test
Following are some NCM-MCI-5.15 Exam Questions for Review
An administrator is deploying a new application to a Nutanix Enterprise Cloud. The application requires a security to prevent unauthorized access. The application also uses many non-standard ports that are unique to it. Security should not be changed for existing applications.
What should the administrator do to meet these requirement?
Refer to the exhibit.
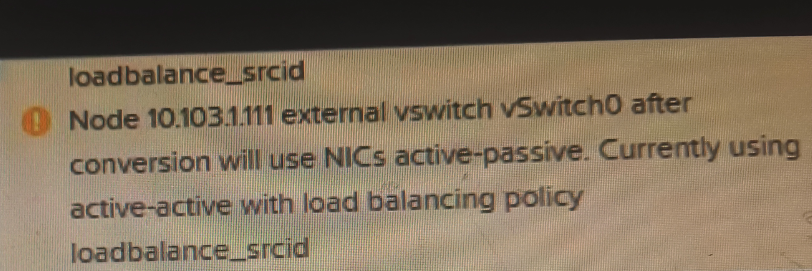
An administrator receive the warning massages shown in the exhibit while validating cluster conversion from EXSi to AHV.
What should the administrator do to address this warning in v Center Server?
After the migration, some SQL queries take longer to execute than prior to migration.
The following SQL best practices were applied while creating the SQL VM on Nutanix:
* 8 vDisks per SQL server VM
* Database and Log files on separate vDisk
* 2 TempDB database drives and 1 TempDB log drive
What should the administrator to do improve the SQL Server performance?
An administrator learns that some security settings in a cluster have been changed. The environment is out of compliance with required policies.
Which function should be used to revert any settings that have changed from the defaults and prevent further violations?
Refer to the exhibit.
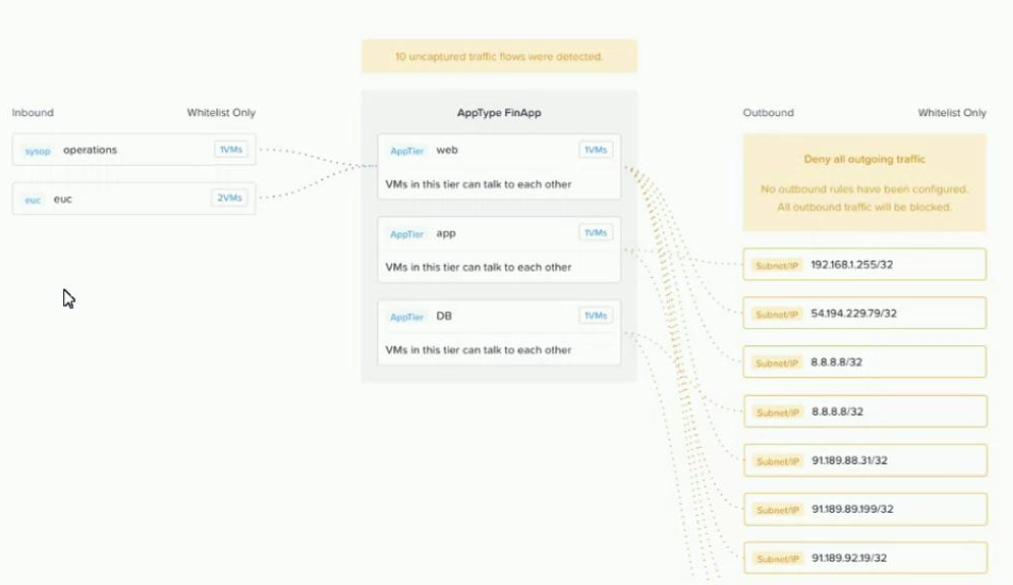
An administrator creates a security policy that isolates their financial application from accessing the Internet When viewing the policy in Prism Central, several connections from the application are outbound to the Internet.
What is causing this issue with the policy?
Unlock All Features of Nutanix NCM-MCI-5.15 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support