
Get HP HPE2-W05 Exam Dumps
HP Implementing Aruba IntroSpect Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

HPE2-W05 Desktop Practice
Test Software
Total Questions : 115

HPE2-W05 Questions & Answers
(PDF)
Total Questions : 115

HPE2-W05 Web Based Self Assessment Practice Test
Following are some HPE2-W05 Exam Questions for Review
The company has a DMZ with an application server where customers can upload and access their product orders. The security admin wants to know how you configure IntroSpect to monitor this server. Should this be part of your plan? (Configure the server in the DMZ as a High Value Asset in
Menu>Configuration>Analytics>Correlator Config>so that IntroSpect will monitor the server for access patterns.)
The company has a DMZ with an application server where customers can upload and access their product orders. The security admin wants to know how you configure IntroSpect to monitor this server. Should this be part of your plan? (List the IP subnet of the DMZ as ''External'' under the Main Menu > Analytics>Global Config>so that alerts for the server will show up as IN-to-OUT traffic.)
While investigating alerts you notice a user entity has triggered a historical alert for Large Internal Data
Download. While investigating the alert, you notice that the download came from a different device than normal for the user. Based on these conditions, is this a possible cause? (This is a classic user account take over pattern.)
Refer to the exhibit.
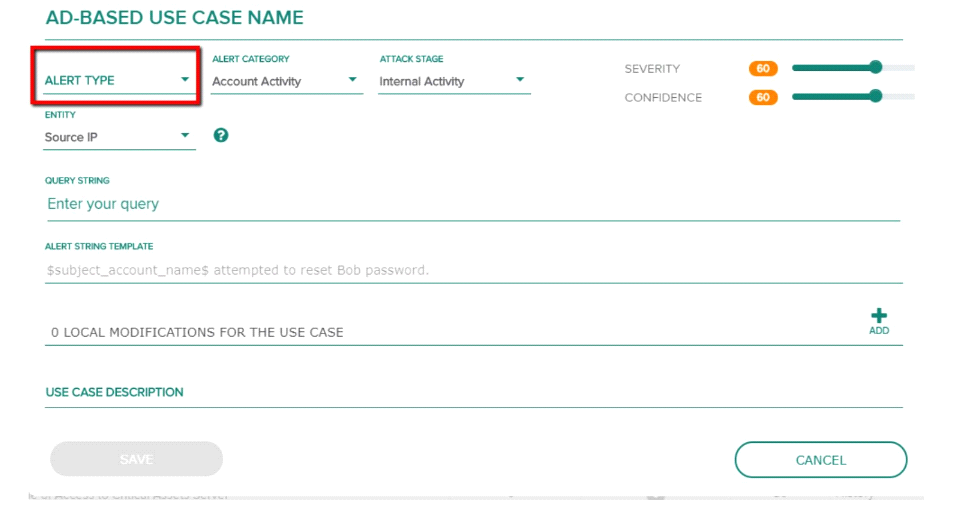
Which alert is not supported by AD-based use case? (Privilege escalation.)
Refer to the exhibit.
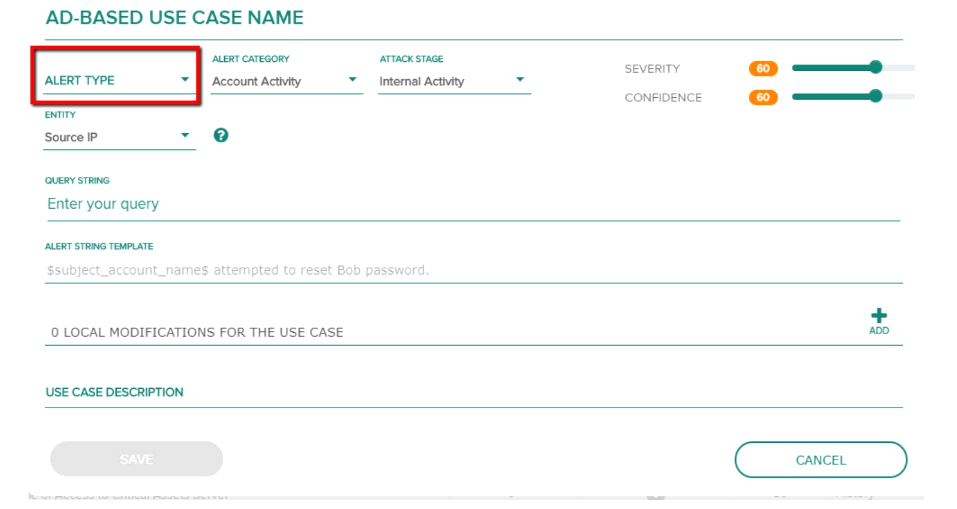
Which alert is not supported by AD-based use case? (Suspicious user login.)
Unlock All Features of HPE2-W05 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support