
Get CIW 1D0-571 Exam Dumps
CIW Web Security Associate Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

1D0-571 Desktop Practice
Test Software
Total Questions : 62

1D0-571 Questions & Answers
(PDF)
Total Questions : 62

1D0-571 Web Based Self Assessment Practice Test
Following are some 1D0-571 Exam Questions for Review
Consider the following diagram:
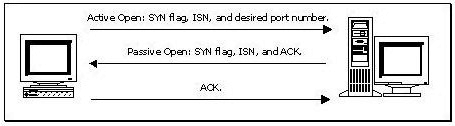
Which of the following best describes the protocol activity shown in the diagram, along with the most likely potential threat that accompanies this protocol?
Which of the following is most likely to address a problem with an operating system's ability to withstand an attack that attempts to exploit a buffer overflow?
At what layer of the OSI/RM does a packet filter operate?
Consider the following image of a packet capture:
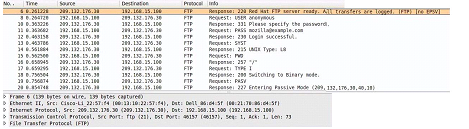
Which of the following best describes the protocol used, along with its primary benefit?
You have been assigned to provide security measures for your office's reception area. Although the company needs to provide security measures, costs must be kept to a minimum. Which of the following tools is the most appropriate choice?
Unlock All Features of CIW 1D0-571 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support