
Get Cisco 350-201 Exam Dumps
Cisco Performing CyberOps Using Core Security Technologies Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

350-201 Desktop Practice
Test Software
Total Questions : 139

350-201 Questions & Answers
(PDF)
Total Questions : 139

350-201 Web Based Self Assessment Practice Test
Following are some 350-201 Exam Questions for Review
Refer to the exhibit.
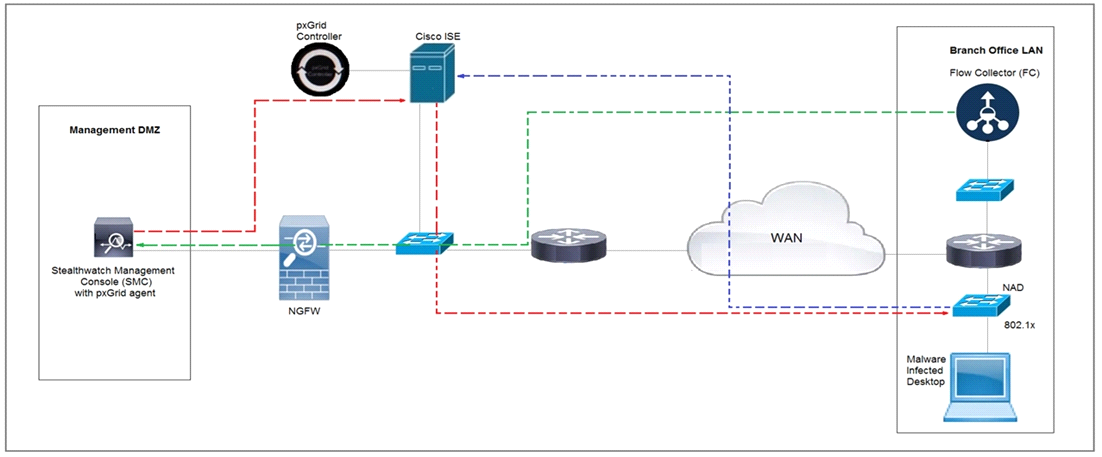
Rapid Threat Containment using Cisco Secure Network Analytics (Stealthwatch) and ISE detects the threat of malware-infected 802.1x authenticated endpoints and places that endpoint into a quarantine VLAN using Adaptive Network Control policy. Which method was used to signal ISE to quarantine the endpoints?
Which bash command will print all lines from the ''colors.txt'' file containing the non case-sensitive pattern ''Yellow''?
Refer to the exhibit.
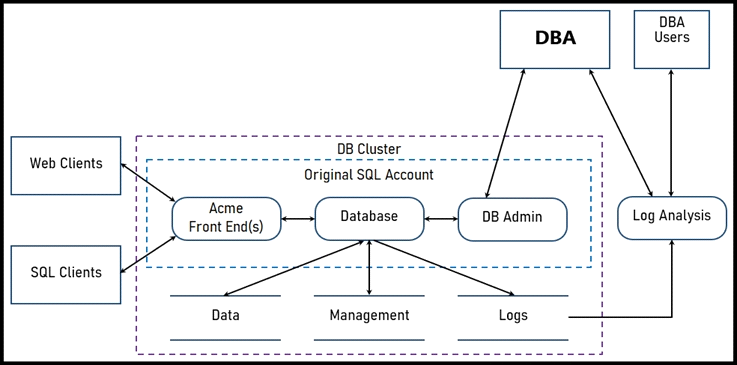
Two types of clients are accessing the front ends and the core database that manages transactions, access control, and atomicity. What is the threat model for the SQL database?
An organization suffered a security breach in which the attacker exploited a Netlogon Remote Protocol vulnerability for further privilege escalation. Which two actions should the incident response team take to
prevent this type of attack from reoccurring? (Choose two.)
A security architect in an automotive factory is working on the Cyber Security Management System and is implementing procedures and creating policies to prevent attacks. Which standard must the architect apply?
Unlock All Features of Cisco 350-201 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support