
Get Fortinet NSE8_812 Exam Dumps
Fortinet NSE 8 - Written Exam Dumps
This Bundle Pack includes Following 3 Formats
Test software
Practice Test
Answers (PDF)

NSE8_812 Desktop Practice
Test Software
Total Questions : 60

NSE8_812 Questions & Answers
(PDF)
Total Questions : 60

NSE8_812 Web Based Self Assessment Practice Test
Following are some NSE8_812 Exam Questions for Review
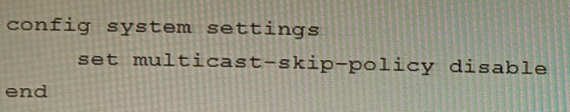
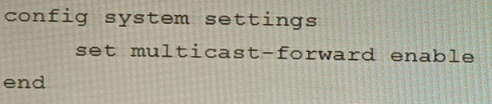
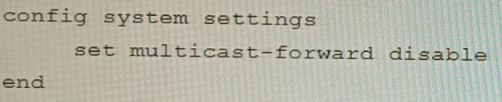
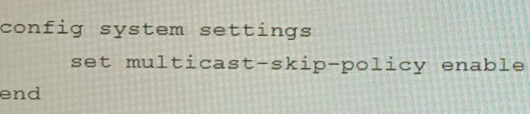
On a FortiGate Configured in Transparent mode, which configuration option allows you to control Multicast traffic passing through the?
A)
B)
C)
D)
You are migrating the branches of a customer to FortiGate devices. They require independent routing tables on the LAN side of the network.
After reviewing the design, you notice the firewall will have many BGP sessions as you have two data centers (DC) and two ISPs per DC while each branch is using at least 10 internal segments.
Based on this scenario, what would you suggest as the more efficient solution, considering that in the future the number of internal segments, DCs or internet links per DC will increase?
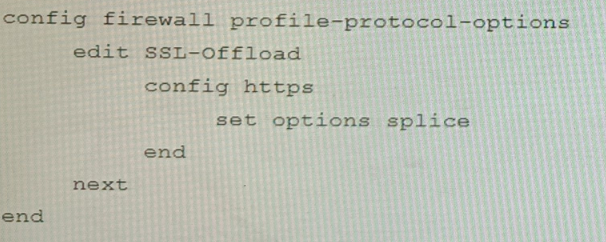
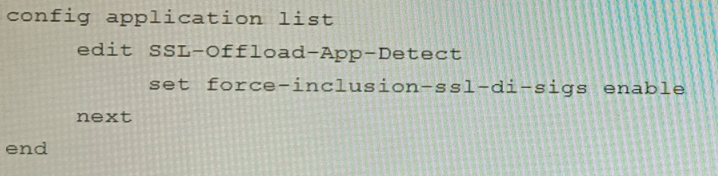
Refer to the exhibits.
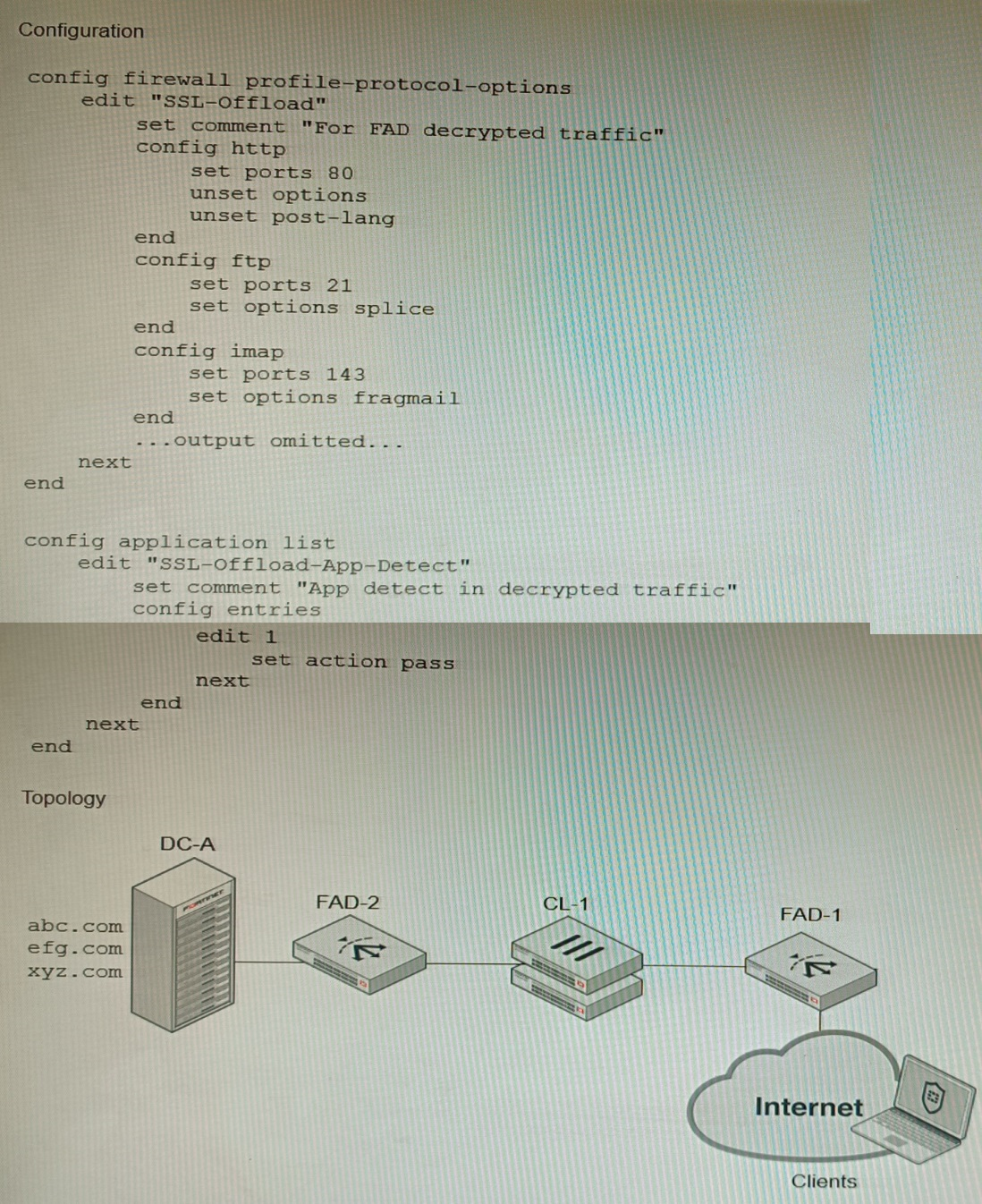
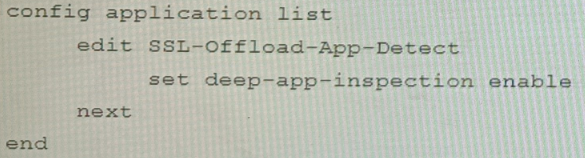
A FortiGate cluster (CL-1) protects a data center hosting multiple web applications. A pair of FortiADC devices are already configured for SSL decryption (FAD-1), and re-encryption (FAD-2). CL-1 must accept unencrypted traffic from FAD-1, perform application detection on the plain-text traffic, and forward the inspected traffic to FAD-2.
The SSL-Offload-App-Detect application list and SSL-Offload protocol options profile are applied to the firewall policy handling the web application traffic on CL-1.
Given this scenario, which two configuration tasks must the administrator perform on CL-1? (Choose two.)
A)
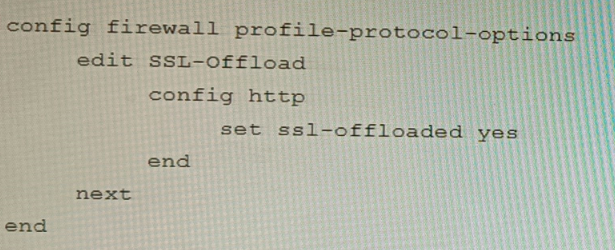
B)
Refer to the exhibits, which show a firewall policy configuration and a network topology.
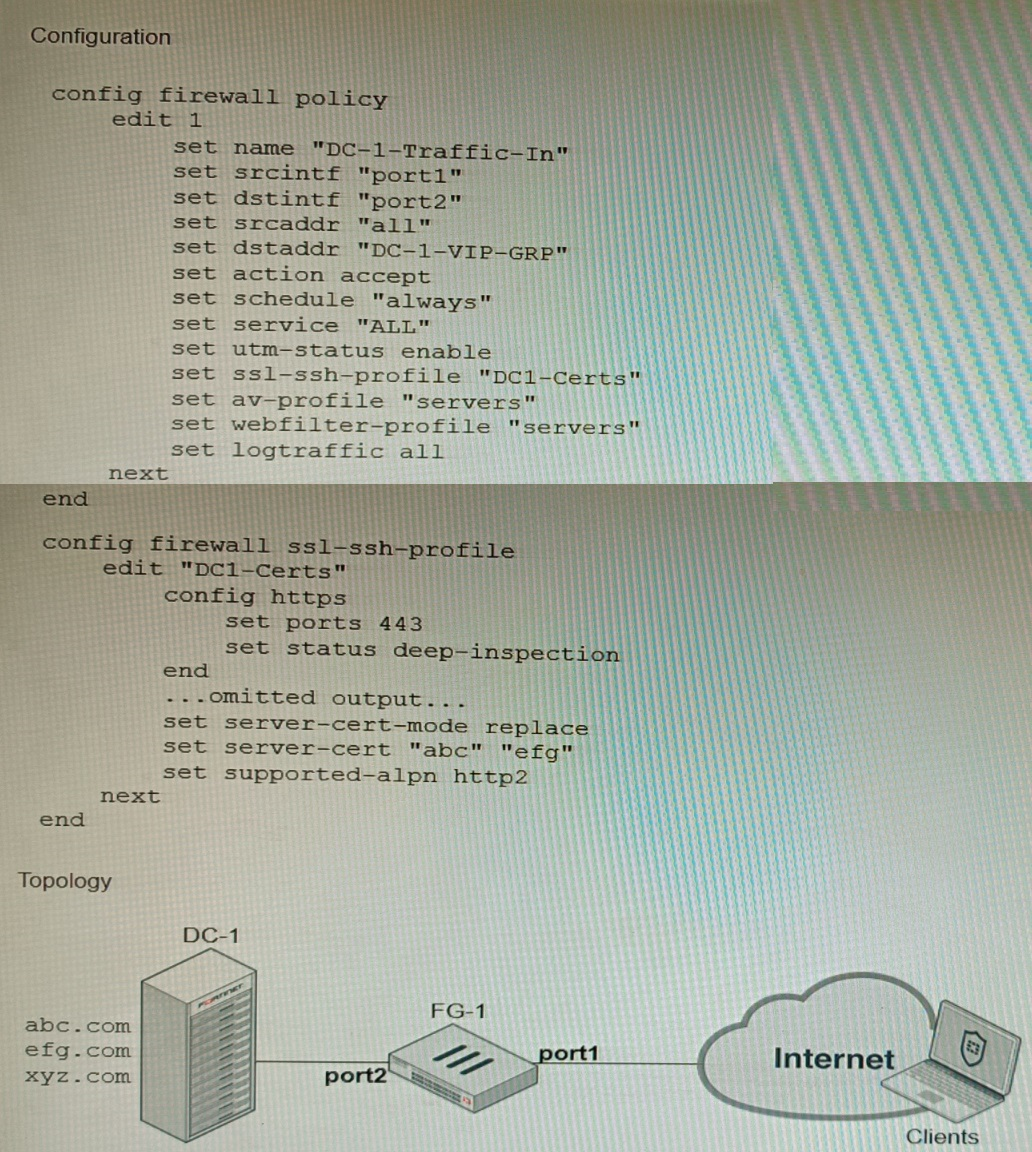
An administrator has configured an inbound SSL inspection profile on a FortiGate device (FG-1) that is protecting a data center hosting multiple web pages-Given the scenario shown in the exhibits, which certificate will FortiGate use to handle requests to xyz.com?
Refer to the exhibit showing the history logs from a FortiMail device.
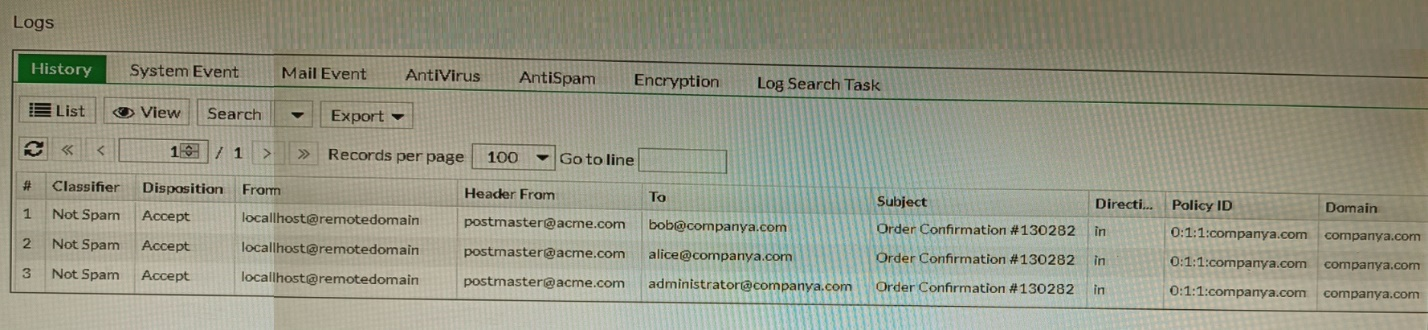
Which FortiMail email security feature can an administrator enable to treat these emails as spam?
Unlock All Features of Fortinet NSE8_812 Dumps Software
Types you want
pass percentage
(Hours: Minutes)
Practice test with
limited questions
Support